Our Blog – The latest News and Information
The latest News and Information from Pearce IT. Every day we are faced with an information overload, getting the information you need and leaving the rest behind is the secret to managing life and stress. That’s why we spend time to read the latest news and filter out the information you dont need to know.
Adversary-in-the-Middle Attacks: How Phishing Sites Steal Your Active Login
You click a link, sign in, approve the MFA prompt, and get on with your day. Completely unaware that someone else just logged into your account at the same moment.That scenario surprises many businesses, particularly those that rely on multi-factor authentication...
The “Session Cookie” Hijack: Why MFA Can’t Always Save You
MFA is a strong front-door lock. But it’s not the only thing that decides whether someone can get in.After you sign in, your browser keeps you logged in using a session token (often stored as a cookie). It’s the digital version of a wristband at an event: once...
The “Legacy Debt” Audit: Identifying the 3 Oldest Risks in Your Server Room
The most dangerous thing in a server room is often the phrase, “Don’t touch that.”It’s usually said with a half-joke and a grimace. It refers to the old box that “still works”, runs something important, and has survived so many fixes and workarounds that nobody...
The “Backup Exit” Strategy: Can You Move Your Data Without the Vendor’s Help?
When you first sign up for a software-as-a-service (SaaS) platform, everything is designed to feel effortless. The problem is that the first real test of a SaaS relationship isn’t the onboarding. It’s the exit. For many small businesses, the front door is...
Micro-SaaS Vetting: The 5-Minute Security Check for Browser Add-ons
Browser add-ons have a funny reputation. They feel “small”. A quick install. A tiny productivity boost. A harmless little helper that lives in your toolbar.But in practice, a browser extension is more like a micro-SaaS vendor sitting inside your browser session. It...
LinkedIn “Social Engineering”: Protecting Your Staff from Fake Recruitment Scams
A fake recruiter message is one of the cleanest social engineering tricks around because it doesn’t look like a trick.That’s why LinkedIn recruitment scams work so well inside real businesses. They don’t arrive as malware. They arrive as a normal conversation...
“Clean Desk” 2.0: Securing Your Home Office from Physical Data Leaks
In the traditional office, a “Clean Desk” policy was a simple habit: shred the sensitive stuff, lock it away, and don’t leave passwords where someone can see them.In 2026, the same idea still matters but the “desk” has changed. For many teams, the home office...
The Essential Checklist for Securing Company Laptops at Home
At home, security incidents don’t look like dramatic movie hacks. They look like stepping away from your laptop during a delivery, or leaving it unlocked while you grab something from another room.Those ordinary moments, repeated over time, are how work devices end...
The 2026 Guide to Uncovering Unsanctioned Cloud Apps
If you want to uncover unsanctioned cloud apps, don’t begin with a policy. Start with your browser history.The cloud environment most businesses actually use rarely matches the one shown on the IT diagram. It’s built through countless small shortcuts: a “just this...
Stop Ransomware in Its Tracks: A 5-Step Proactive Defense Plan
Ransomware isn’t a jump scare. It’s a slow build.In many cases, it begins days, or even weeks, before encryption, with something mundane, like a login that never should have succeeded.That’s why an effective ransomware defense plan is about more than deploying...
How to Run a “Shadow AI” Audit Without Slowing Down Your Team
It usually starts small. Someone uses an AI tool to refine a difficult email. Someone enables an AI add-on inside a SaaS app because it promises to save an hour a week. Someone pastes a paragraph into a chatbot to “make it sound better.”Then it becomes routine.And...
A Small Business Roadmap for Implementing Zero-Trust Architecture
Most small businesses aren’t breached because they have no security at all. They’re breached because a single stolen password becomes a master key to everything else.That’s the flaw in the old “castle-and-moat” model. Once someone gets past the perimeter, they can...
5 Security Layers Your MSP Is Likely Missing (and How to Add Them)
Most small businesses aren’t falling short because they don’t care. They’re falling short because they didn’t build their security strategy as one coordinated system. They added tools over time to solve immediate problems, a new threat here, a client request...
Zero-Trust for Small Business: No Longer Just for Tech Giants
Think about your office building. You probably have a locked front door, security staff, and maybe even biometric checks. But once someone is inside, can they wander into the supply closet, the file room, or the CFO’s office? In a traditional network, digital...
The Supply Chain Trap: Why Your Vendors Are Your Biggest Security Risk
You invested in a great firewall, trained your team on phishing, and now you feel secure. But what about your accounting firm’s security? Your cloud hosting provider? The SaaS tool your marketing team loves? Each vendor is a digital door into your business. If they...
The “Insider Threat” You Overlooked: Proper Employee Offboarding
Imagine a former employee, maybe someone who didn’t leave on the best terms. Their login still works, their company email still forwards messages, and they can still access the project management tool, cloud storage, and customer database. This isn’t a hypothetical...
The 2026 Hybrid Strategy: Why “Cloud-Only” Might Be a Mistake
Since cloud computing became mainstream, promising agility, simplicity, offloaded maintenance, and scalability, the message was clear: “Move everything to the cloud.” But once the initial migration wave settled, the challenges became apparent. Some workloads thrive...
Managing “Cloud Waste” as You Scale
When you first move your data and computing resources to the cloud, the bills often seem manageable. But as your business grows, a worrying trend can appear. Your cloud expenses start climbing faster than your revenue. This is not just normal growth, it is a...
Beyond Chatbots: Preparing Your Small Business for “Agentic AI” in 2026
AI chatbots can answer questions. But now picture an AI that goes further, updating your CRM, booking appointments, and sending emails automatically. This isn’t some far-off future. It’s where things are headed in 2026 and beyond, as AI shifts from reactive tools...
The Server Refresh Deadline: Why Windows Server 2016’s End of Support Should Drive Your Cloud Migration Plan
Time moves fast in the world of technology, and operating systems that once felt cutting-edge are becoming obsolete. With Microsoft having set the deadline for Windows Server 2016 End of Support to January 12, 2027, the clock is ticking for businesses that use this...
The MFA Level-Up: Why SMS Codes Are No Longer Enough (and What to Use Instead)
For years, enabling Multi-Factor Authentication (MFA) has been a cornerstone of account and device security. While MFA remains essential, the threat landscape has evolved, making some older methods less effective.The most common form of MFA, four- or six-digit...
The Daily Cloud Checkup: A Simple 15-Minute Routine to Prevent Misconfiguration and Data Leaks
Moving to the cloud offers incredible flexibility and speed, but it also introduces new responsibilities for your team. Cloud security is not a “set it and forget it” type task, small mistakes can quickly become serious vulnerabilities if ignored.You don’t need to...
The “Deepfake CEO” Scam: Why Voice Cloning Is the New Business Email Compromise (BEC)
The phone rings, and it’s your boss. The voice is unmistakable; with the same flow and tone you’ve come to expect. They’re asking for a favor: an urgent wire transfer to lock in a new vendor contract, or sensitive client information that’s strictly confidential....
Securing the ‘Third Place’ Office: Policy Guidelines for Employees Working from Coffee Shops and Coworking Spaces
The modern office extends far beyond traditional cubicles or open-plan spaces. Since the concept of remote work became popularized in the COVID and post-COVID era, employees now find themselves working from their homes, libraries, bustling coffee shops, and even...
AI’s Hidden Cost: How to Audit Your Microsoft 365 Copilot Usage to Avoid Massive Licensing Waste
Artificial Intelligence (AI) has taken the business world by storm, pushing organizations of all sizes to adopt new tools that boost efficiency and sharpen their competitive edge. Among these tools, Microsoft 365 Copilot rises to the top, offering powerful...
The Smarter Way to Vet Your SaaS Integrations
Your business runs on a SaaS (software-as-a-service) application stack, and you learn about a new SaaS tool that promises to boost productivity and streamline one of your most tedious processes. The temptation is to sign up for the service, click “install,” and...
How to Use Conditional Access to Grant and Revoke Contractor Access in 60 Minutes
Managing contractor logins can be a real headache. You need to grant access quickly so work can begin, but that often means sharing passwords or creating accounts that never get deleted. It’s the classic trade-off between security and convenience, and security...
How to Implement Zero Trust for Your Office Guest Wi-Fi Network
Guest Wi-Fi is a convenience your visitors expect and a hallmark of good customer service. But it’s also one of the riskiest points in your network. A shared password that’s been passed around for years offers virtually no protection, and a single compromised guest...
6 Ways to Prevent Leaking Private Data Through Public AI Tools
We all agree that public AI tools are fantastic for general tasks such as brainstorming ideas and working with non-sensitive customer data. They help us draft quick emails, write marketing copy, and even summarize complex reports in seconds. However, despite the...
5 Ways to Implement Secure IT Asset Disposition (ITAD) in Your Small Business
Even the most powerful IT hardware today will eventually become outdated or faulty and will need to be retired. However, these retired servers, laptops, and storage devices hold a secret: they contain highly sensitive data. Simply throwing them in the recycling bin...
3 Simple Power Automate Workflows to Automatically Identify and Terminate Unused Cloud Resources
The cloud makes it easy to create virtual machines, databases, and storage accounts with just a few clicks. The problem is, these resources are often left running long after they’re needed. This “cloud sprawl,” the unmanaged growth of cloud resources, can quietly...
Your 2025 Privacy Compliance Checklist and What You Need to Know About the New Data Laws
Privacy regulations are evolving rapidly, and 2025 could be a pivotal year for businesses of all sizes. With new state, national, and international rules layering on top of existing requirements, staying compliant is no longer optional. A basic policy won’t...
The SMB Guide to Making Your Website and Documents Digitally Accessible
Have you ever thought about how many potential customers leave your website because of accessibility issues? It’s not just a guess. A UK Click-Away Pound survey found that 69% of disabled internet users leave websites that aren’t accessible. For small and medium...
The Hidden Risk of Integrations: A Checklist for Vetting Third-Party Apps (API Security)
Modern businesses depend on third-party apps for everything from customer service and analytics to cloud storage and security. But this convenience comes with risk, every integration introduces a potential vulnerability. In fact, 35.5% of all recorded breaches in...
The AI Policy Playbook: 5 Critical Rules to Govern ChatGPT and Generative AI
ChatGPT and other generative AI tools, such as DALL-E, offer significant benefits for businesses. However, without proper governance, these tools can quickly become a liability rather than an asset. Unfortunately, many companies adopt AI without clear policies or...
How to Use a Password Manager and Virtual Cards for Zero-Risk Holiday Shopping
Have you ever been concerned about your credit card or personal data getting stolen while shopping online? You’re not alone. Each holiday season, as millions of shoppers flock online for convenience, hackers ramp up their activity. The Federal Trade Commission...
Beyond Licensing: How to Stop Wasting Money onYour Microsoft 365 Security and Copilot Add-Ons
Microsoft 365 is a powerful platform that helps a business in many ways. It boosts collaboration and streamlines operations, among other benefits. However, many companies waste money on unnecessary licenses and features that are not fully used. Fortunately,...
7 Ways Using AI for Work Can Get Complicated
AI is going to change how we work. It can make some tasks easier. But it can also cause problems. Let’s look at some ways AI can make work tricky.What is AI and how does it affect work?AI stands for Artificial Intelligence. The computer systems are actually able to...
Ultimate Guide to Encryption Methods
Encryption is a method of securing information. It converts readable data into secret code. Only the right key can decode it. This guide will help you understand different encryption methods.What is Encryption?Encryption is like a secret language. It converts...
How is Your Cyber Hygiene? Essential Tips For 2025
Cyber hygiene is super important. It’s like brushing your teeth but for your online life. Good cyber habits help keep you safe from hackers on the internet. Let’s check some easy ways to stay safe online in 2025. What is Cyber Hygiene?Cyber hygiene means...
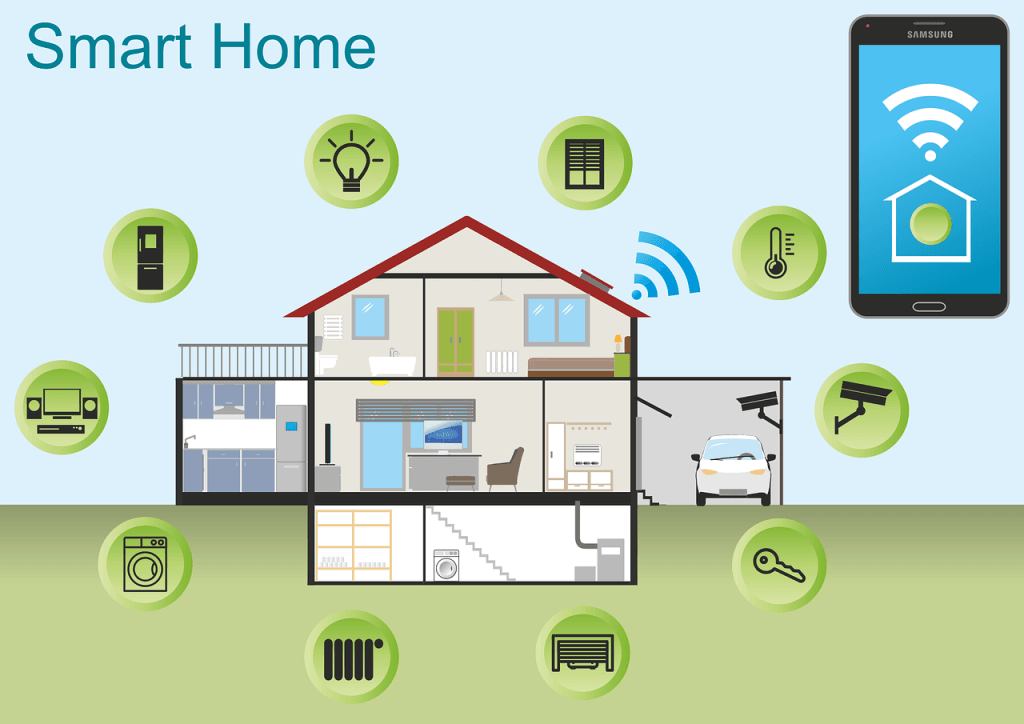
10 Tips For a Seamless Smart Home Experience
Smart homes make life easier. But setting one up can be tricky. Here’s how to make a smooth smart home system.What is a Smart Home?A smart home uses technology to control many parts of life. This includes turning lights on and off and unlocking doors. You can...
What is Threat Exposure Management (TEM)?
Threat Exposure Management (TEM) is an important cybersecurity tool. It helps organizations find and fix weak spots in their digital systems. TEM outsmarts hackers before they break into your network.Importance of TEMCyber attacks keep getting worse. Hackers always...
How Password Managers Protect Your Accounts
Passwords unlock our digital lives. We use them for email, bank accounts, and more. Remembering all these passwords is hard. Password managers help us keep our accounts safe and make our lives easier.What is a Password Manager?A password manager keeps all your...
Innovative Solutions to IoT Device Security
The Internet of Things is growing day by day. More devices are connecting to the internet. And with that growth comes new security risks.Let’s look at some new ways to keep your IoT devices safe.What are the security risks for IoT devices?IoT devices are vulnerable...
5 New Trends from a Study on the State of AI at Work
The pace of technological advancement is accelerating. This is not news to anyone wading through the ChatGPT craze. Artificial intelligence (AI) is at the forefront of this revolution. We are swiftly seeing companies adopting AI solutions. Even more rapidly are...
Guide to Smart Windows 11 Settings to Boost Your Productivity
The newest Windows OS is fast gaining ground on Windows 10. As of August 2024, Windows 11 had over 31% of the Windows market share. That is bound to increase fast as Windows 10 retires in 2025.Already upgraded to the new operating system or planning to soon? Then,...
Protect Yourself: 8 Steps to Take When You Get a Notice Your Data Was Breached
When it happens, you feel powerless. You get an email or letter from a business saying someone breached your data. It happens all too often today.Data breaches happen at banks, online sites like Facebook, and ecommerce stores. Not only that, but governments are...
How Can Small Businesses Embrace the Cashless Revolution?
The world has gone digital. We see it everywhere people shop for goods and services. Cash, check, or debit used to be the norm. Now, there are payment wallets that people expect businesses to accept. They include things like Apple Pay, Google Pay, PayPal and...
Watch Out for Google Searches – “Malvertising” Is on the Rise!
There are many types of malware. One of the most common is called “malvertising.” It crops up everywhere. Including social media sites and websites. You can also see these malicious ads on Google searches.Two things are making malvertising even more dangerous. One...
Cyber Experts Say You Should Use These Best Practices for Event Logging
Today’s businesses are no stranger to the word cybersecurity. They are facing a growing wave of cyberattacks. These come from ransomware to sophisticated phishing schemes. How do you stand ahead of these threats? A strong cybersecurity strategy is essential. One...
7 Great Examples of How AI is Helping Small Businesses
Artificial Intelligence is no longer a technology reserved for companies with big budgets. Today, small businesses can access AI tools that help in several ways. Such as streamlining operations, improving customer experiences, and boosting profits. The rise of...
Top Technologies Transforming Customer Service Today
Customer service is at the heart of any successful business. Customer expectations continue to evolve. Companies must evolve strategies and tools used to meet those expectations. 55% of customers like self-serve customer service over speaking to a...
Data Breach Damage Control: Avoid These Pitfalls
Data breaches are an unfortunate reality for businesses of all sizes. When a breach occurs, the immediate response is critical. How a company manages the aftermath can significantly impact its reputation. As well as financial stability and legal standing.The...
Copilot in Teams – New Features, Agents & More
Microsoft Teams continues to evolve. It is a powerful hub for collaboration and communication in the modern workplace. With the integration of AI-driven Copilot, Teams is pushing the boundaries. It’s innovating how we interact with technology to streamline...
Navigating the Challenges of Data Lifecycle Management
Data is one of the most valuable assets a business can have. Managing this data throughout its lifecycle can be challenging. Data lifecycle management (DLM) refers to several processes and policies. They govern the handling, storage, and eventual disposal of...
6 Simple Steps to Enhance Your Email Security
Email is a fundamental communication tool for businesses and individuals alike. But it’s also a prime target for cybercriminals. Cyberattacks are increasing in sophistication. This means enhancing your email security has never been more critical.Ninety-five percent...
8 Strategies for Tackling “Technical Debt” at Your Company
Did your company’s software system once seem sleek and nimble? But now it resembles a tangled web of shortcuts, patches, and workarounds. Welcome to the realm of technical debt. It’s a silent saboteur that accumulates over time, threatening your efficiency.What Is...
Enhancing Employee Performance with a Mobile-Optimized Workspace
In the whirlwind of today’s business landscape, adaptability reigns supreme. Today’s workspaces transcend physical boundaries. Employees work and collaborate seamlessly from anywhere. Whether they’re sipping coffee at a local café or lounging on their...
Essential Settings to Maximize Your Microsoft 365 Experience
Microsoft 365 is a powerful suite of tools. It helps to enhance productivity and collaboration. This is especially true for small to mid-sized businesses (SMBs). But to get the most out of Microsoft 365, it’s important to optimize its settings. Otherwise, you may...
Why Securing Your Software Supply Chain is Critical
In today’s world, everything’s connected. That includes the software your business relies on. Whether you’ve installed that software locally or use it in the cloud.Protecting the entire process that creates and delivers your software is very important. From...
Don’t Be a Victim: Common Mobile Malware Traps
Your smartphone is a digital wallet, communication hub, and personal assistant. All rolled into one portable device. It’s packed with sensitive data, from financial information to personal photos. This makes it a prime target for cybercriminals. Mobile malware...
6 Helpful Tips to Troubleshoot Common Business Network Issues
A business network is the lifeblood of operations. It’s the digital artery that pumps data through your organization. It enables everything from email to critical applications and cloud services. When problems sever that lifeline, the consequences can be...
What Things Should You Consider Before Buying a Used Laptop?
Buying a used laptop can be a great way to save money. But it comes with risks. You need to be careful and thorough in your evaluation. Otherwise, you could end up wasting your money. You can’t only look at the outside when evaluating technology. This guide...
Top 6 Smart Office Trends to Adopt for an Improved Workflow
The office landscape is undergoing a dramatic transformation. Gone are the days of sterile cubicles and monotonous routines. Today’s smart offices are hubs of innovation. They’re designed to empower employees, optimize workflows, and foster collaboration.This...
Windows 10: The Final Countdown – It’s Time to Upgrade Your PC
Windows 10 has served us well. But its time is running out. Microsoft plans to end support for Windows 10 on October 14, 2025. This means no more security updates, no more patches, and no more support. It’s time to upgrade to Windows 11. This is especially...
8 Tips for Safeguarding Your Gadgets While Traveling
Traveling with technology has become a necessity. Whether for work, communication, or entertainment, we rely heavily on our devices. But traveling exposes these gadgets to various risks. Theft, damage, and loss are common concerns. We’ve put together some...
Unmasking the True Price of IT Downtime
Imagine this: you walk into your office on a busy Monday morning, ready to tackle the week. But something’s wrong. Computers are unresponsive. Phones are silent. The internet is a ghost town. Your business has come to a grinding halt – victim of an IT...
Streamlining Success: A Guide to Task Automation for Small Enterprises
Running a small business is a whirlwind. You juggle a million tasks and wear countless hats. You also constantly fight the clock. What if you could reclaim some of that precious time? Enter task automation. It’s your secret weapon for streamlining your...
Phishing 2.0: How AI is Amplifying the Danger and What You Can Do
Phishing has always been a threat. Now, with AI, it’s more dangerous than ever. Phishing 2.0 is here. It’s smarter, more convincing, and harder to detect. Understanding this new threat is crucial. A recent study found a 60% increase in AI-driven phishing...
Unified Smart Homes: How Matter is Setting a New Standard
Is your smart home turning into a smart mess? Do your smart office devices speak different languages? You’re not alone. The current smart home and office technology landscape is riddled with incompatibility issues. This forces you to juggle several apps and...
Digital Defense: Essential Security Practices for Remote Workers
The rise of remote work has redefined the modern workplace. Gone are the days of rigid office schedules and commutes. But with this flexibility comes a new set of challenges – cybersecurity threats. Remote work environments often introduce vulnerabilities to your...
Tech-Savvy Workspaces: How Technology Drives Office Productivity
Gone are the days of paper-laden desks and rows of filing cabinets. The modern office is a hub of innovation. Technology plays a starring role in this transformation. The right tech tools can significantly boost your team’s productivity. Including...
AI Data Breaches are Rising! Here’s How to Protect Your Company
Artificial intelligence (AI) is rapidly transforming industries. It offers businesses innovative solutions and automation capabilities. But with this progress comes a growing concern: AI data breaches. As AI becomes more integrated into our systems, the risks...
7 Important Considerations Before You Buy Smart Home Tech
Smart homes seem like something straight out of a sci-fi movie. They have lights that respond to your voice commands and thermostats that auto-adjust. Not to mention robot vacuums that clean your floors while you relax.It’s all very tempting. But before you...
Why Continuous Monitoring is a Cybersecurity Must
Imagine this: you leave your house for vacation. You live in a shady neighborhood but feel confident your locks are secure, but you also don’t checkthem daily. Are they really locked and safe? A tiny crack or hidden weakness could have occurred. It’s a disaster...
A Simple Guide to the Updated NIST 2.0 Cybersecurity Framework
Staying ahead of threats is a challenge for organizations of all sizes. Reported global security incidents grew between February and March of 2024. They increased by 69.8%. It’s important to use a structured approach to cybersecurity. This helps to protect your...
Hot off the Digital Presses… Learn About Microsoft Copilot for Finance
Microsoft Copilot has been heading up the business AI charge. It’s used in Word, Excel, Edge, Windows, and more. This genAI-powered app is also showing up invarious function-related activities. The latest of which is finance processes.Microsoft Copilot for Finance...
iPhone Running Slow? Speed It up with One of These Tips
Let’s face it, iPhones are amazing devices. But even the sleekest, most powerful iPhone can succumb to the dreaded slowdown. Apps take forever to load and scrolling feels sluggish. Pretty soon, simple tasks become frustrating ordeals.If your iPhone has gone...
Is Your Business Losing Money Because Employees Can’t Use Tech?
Shiny new tech can be exciting! It promises increased efficiency, happier employees, and a competitive edge. It’s also necessary to stay competitive in today’s technology-driven business world.But that promise can turn into a financial nightmare if you neglect two...
10 Easy Steps to Building a Culture of Cyber Awareness
Cyberattacks are a constant threat in today’s digital world. Phishing emails, malware downloads, and data breaches. They can cripple businesses and devastate personal lives.Employee error is the reason many threats get introduced to a business network. A lack...
What Were the Coolest Consumer Products Showcased at CES 2024?
The annual Consumer Electronics Show (CES) was an exciting one this year. It left us with a mind-blowing glimpse into the future of technology. CES 2024 showcased a smorgasbord of cutting-edge gadgets. Including transparent TVs and robot pet buddies. These gadgets...
Smart Tips for Building a Smart Home on a Budget
Imagine a world where your lights turn on automatically as you walk in the door. Your coffee starts brewing before you even crawl out of bed. A simple voice command adjusts the temperature to your perfect setting.This is no longer just something out of a sci-fi...
Guide to Improving Your Company’s Data Management
Data is the lifeblood of modern businesses. It fuels insights, drives decision-making, and ultimately shapes your company’s success. But in today’s information age, data can quickly become overwhelming.Scattered spreadsheets, siloed databases, and...
Don’t Risk It! Why You Shouldn’t Skip Vulnerability Assessments
Cyber threats are a perpetual reality for business owners. Hackers are constantly innovating. They devise new ways to exploit vulnerabilities in computer systems and networks.For businesses of all sizes, a proactive approach to cybersecurity is essential. One of...
7 Common Pitfalls When Adopting Zero Trust Security
Zero Trust security is rapidly transforming the cybersecurity landscape. It moves away from traditional perimeter-based security models. In this approach, every connection attempt is continuously verified before granting resource access.56% of global organizations...
4 Ways Small Businesses Can Leverage Copilot for Microsoft 365
What are some of the key differentiators that can propel small businesses forward? They include efficiency, productivity, and innovation. Microsoft has expanded the availability of one of its most dynamic tools to SMBs. A tool that can be a real game-changer for...
Introducing the New Microsoft Planner (Everything You Need to Know)
Calendars, task lists, and project planning are important business tools. Many people use Microsoft’s apps to power these processes. Including Planner, Microsoft To Do, and Project for the web.These tools help keep processes on track and enable task accountability....
How to Properly Deploy IoT on a Business Network
The Internet of Things (IoT) is no longer a futuristic concept. It’s rapidly transforming industries and reshaping how businesses operate. IoT is a blanket term to describe smart devices that are internet enabled. One example is smart sensors monitoring...
Here Are 5 Data Security Trends to Prepare for in 2024
With cyber threats evolving at an alarming pace, staying ahead of the curve is crucial. It’s a must for safeguarding sensitive information. Data security threats are becoming more sophisticated and prevalent. The landscape must change to keep up. In 2024, we can...
Google & Yahoo’s New DMARC Policy Shows Why Businesses Need Email Authentication… Now
Have you been hearing more about email authentication lately? There is a reason for that. It’s the prevalence of phishing as a major security threat. Phishing continues as the main cause of data breaches and security incidents. This has been the case for many...
Beware of Deepfakes! Learn How to Spot the Different Types
Have you ever seen a video of your favorite celebrity saying something outrageous? Then later, you find out it was completely fabricated? Or perhaps you’ve received an urgent email seemingly from your boss. But something felt off.Welcome to the world of...
10 Most Common Smart Home Issues (and How to Fix Them)
Back when you were a kid, living in a “smart home” probably sounded futuristic. Something out of Back to the Future II or The Jetsons. Well, we don’t yet have flying cars, but we do have video telephones as well as smart refrigerators and voice-activated lights.But...
What Is Microsoft Security Copilot? Should You Use It?
It can be challenging to keep up with the ever-evolving cyber threat landscape. Companies need to process large amounts of data. As well as respond to incidents quickly and effectively. Managing an organization’s security posture is complex.That’s where...
Smart Tactics to Reduce Cloud Waste at Your Business
Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. But cloud services also come with a downside: cloud waste.Cloud waste is the unnecessary spending of resources and money on cloud services. These...
Eye-opening Insights from the 2023 Annual Cybersecurity Attitudes and Behaviors Report
We are living in an era dominated by digital connectivity. You can’t overstate the importance of cybersecurity. As technology advances, so do the threats that lurk in the online world.Often, it’s our own actions that leave us most at risk of a cyberattack or...
Be Careful When Scanning QR Codes – There’s a New Scam Going Around!
QR codes are everywhere these days. You can find them on restaurant menus, flyers, and posters. They’re used both offline and online. QR codes are convenient and easy to use. You just scan them with your smartphone camera. You’re then directed to a link, a coupon,...
9 Signs That Your Smart Home Device Has Been Hacked
Smart home devices are becoming more popular and convenient. But they also pose some serious security risks. Hackers can target these devices to access your personal information. As well as spy on your activities or cause damage to your home.Often the dangers of...
5 Cybersecurity Predictions for 2024 You Should Plan For
Cybersecurity is a constantly evolving field. There are new threats, technologies, and opportunities emerging every year. As we enter 2024, organizations need to be aware of current and future cyber threats. Businesses of all sizes and sectors should plan...
Workspaces, a VPN & More – Learn the Newest Microsoft Edge Features
Microsoft Edge continues to redefine user experiences. This is due to Microsoft’s commitment to innovation. The latest updates bring a host of features. These are designed to enhance productivity, security, and browsing satisfaction.Chrome may have been number one...
These 7 AI Trends Are Sweeping the Cybersecurity Realm
Relentless digital innovation has defined the last few years. The symbiotic relationship between AI and cybersecurity has become pivotal especially when it comes to safeguarding sensitive information and digital assets.As cyber threats evolve in complexity, AI has...